1. The Illusion of Control: Digital Gaslighting in the Modern Browser
We have all been there: a desperate, repetitive clicking of the “Back” button that yields nothing but the same unwanted page, or the sudden, cold realization that a website is anticipating your needs with an intimacy that feels less like service and more like surveillance. This isn’t just a glitch; it is “digital gaslighting.”
While we perceive our web browser as a loyal agent—a tool under our direct command—the architecture of the modern web tells a darker story. Behind the glass, clandestine scripts execute in the shadows of your browser’s Document Object Model (DOM), facilitating “privacy-violating information flows” and “dark patterns.” These are not accidental design flaws; they are strategic exploitations intended to override user intent. In the current landscape, while you think you are navigating the web, the web is frequently navigating you through invisible JavaScript processes designed to track, trap, and monetize your every move.
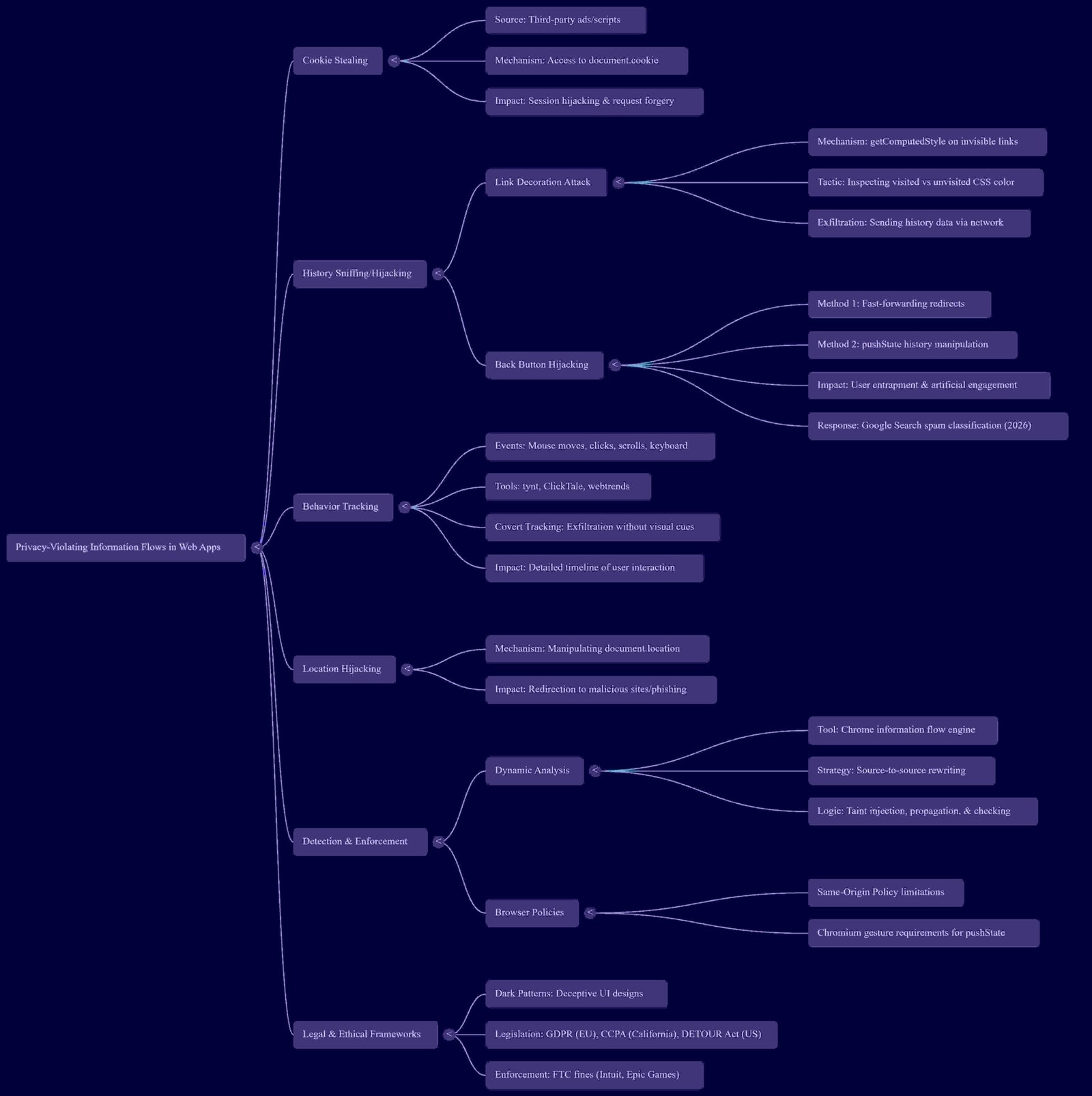
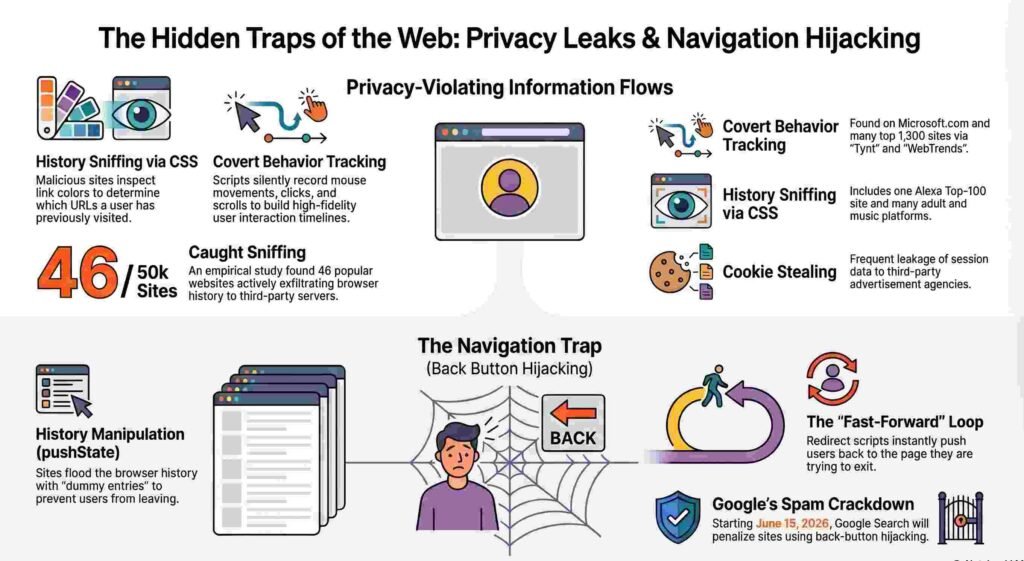
2. The Origin Story: History Sniffing via Link Colors
The betrayal of the browser began with a surprisingly low-tech exploit. In what we might call the “origin story” of browser betrayal, researchers led by Hovav Shacham at the University of California, San Diego, exposed a vulnerability called “History Sniffing.” This technique exploits the fundamental way browsers display links: typically blue for unvisited and purple for visited.
By using JavaScript to programmatically inspect the CSS style properties of a link—specifically its color—a malicious script can determine if a user has visited a specific URL. The attacker creates thousands of hidden links to sensitive destinations (banking portals, medical forums, or adult sites) in a hidden part of the page and “sniffs” the color to reconstruct the user’s private history.
The Shacham study revealed that this wasn’t a fringe exploit; it was found on 46 of the Alexa top 50,000 sites, including a top-100 site. While modern browsers have since mitigated this specific “purple link” vulnerability, the mindset it birthed—using the browser’s own rendering logic to exfiltrate data—remains the blueprint for today’s sophisticated hijacking.
“In JavaScript, the attacker creates a link to the target URL in a hidden part of the page, and then uses the browser’s DOM interface to inspect how the link is displayed. If the link is displayed as a visited link, the target URL is in the user’s history.”
3. Beyond the Click: The Architecture of Attention Tracking
As a strategist, I look for the discrepancy between user expectation and technical reality. Most users understand that a “click” is an intentional data-sharing event. However, few realize that simply moving their mouse or scrolling a page creates a “high-fidelity timeline” of their session that is routinely exfiltrated to remote servers.
This “Behavior Tracking” allows sites to monitor your “attention” with surgical precision. Major sites, including Microsoft’s, have been observed tracking mouse movements to compute interaction statistics. Perhaps more alarming is the use of libraries like “tynt,” which monitor clipboard events. When you copy text from a page, the script “calls home” to log the event. This represents a massive ethical violation: your clipboard often contains the most sensitive data—passwords, private addresses, or financial details—yet it is being monitored by clandestine scripts without a hint of visual notification.
The High-Fidelity Timeline By attaching event handlers to every scroll, mouse-over, and keystroke, websites build a minute-by-minute record of your digital behavior. This data is then used to generate “heat maps,” effectively turning your private browsing session into a laboratory for psychological optimization.
4. Digital Roach Motels: The Technical Architecture of the Back-Button Trap
We call them “Digital Roach Motels”—sites that are easy to enter but nearly impossible to leave. This is “Back-Button Hijacking,” a deceptive practice that breaks the fundamental contract of the browser. According to the WICG and industry analysis, this trap is constructed through two primary mechanisms:
- Redirect Loops: A site employs an intermediate landing page that instantly redirects the user to the target content. When you click “Back,” you land on the intermediate page, which immediately fires the redirect again, effectively pinning you to the site.
- History Manipulation: Using the HTML5
pushStatecommand, scripts can “stuff” the browser history with dummy entries. Even if you stay on one page, the script adds new layers to your history stack.
This results in what Google’s Kenji Baheux describes as “guaranteed frustration.” Because these scripts automate what should be manual human actions, the history entries are processed faster than a human can react. You either “undershoot” the exit and remain trapped, or “overshoot” in a panic, landing several sites back in your history.
“Typically, the History get stuffed with multiple dummy entries that fast-forward the user back to the page they wanted to leave… the user can’t wait for a visual confirmation to know when to stop hitting the back button.”
5. Gaming the System: Navboost and the Irony of “Happiness”
Why do developers risk such intense user vitriol? The answer lies in Google’s internal ranking signals, specifically a system known as “Navboost.” Navboost tracks 13 months of interaction data to measure “user happiness.” To a machine, a user who stays on a page for five minutes is “engaged.”
Back-button hijacking is a direct attempt to “hack” Navboost by artificially extending session duration. By trapping you, the site forces a metric that looks like “engagement” to an algorithm but is actually “rage” in the real world. As SEO strategist Glenn Gabe notes, “Hell hath no fury like a user scorned.” There is a profound irony here: a site may temporarily boost its ranking by faking user happiness, even as it destroys its brand reputation among the human beings it ostensibly serves.
6. The June 2026 Ultimatum: The Browser as User Advocate
The era of the hijacked back button has been issued a death warrant. Google has announced that back-button hijacking will be classified as a “malicious practice” under its spam policies, leading to manual actions and automated demotions in search results.
The enforcement deadline is set for June 15, 2026.
Technically, this marks a historic pivot. Google is moving toward a model where browsers will ignore any history entry that was not generated by a “user gesture”—meaning a physical click or tap. By doing so, the browser is shifting from a “dumb executor” of code to a “user advocate.” It is essentially telling site owners that the browser belongs to the person behind the screen, not the script running on the page. Site owners now have a narrow window to audit their third-party libraries and ad platforms to ensure they aren’t inadvertently employing these toxic tactics.
7. Conclusion: Toward a More Transparent Web
These developments signal a long-overdue shift in the balance of power. For too long, the “invisible” web has been a playground for deceptive design and clandestine tracking. The move to penalize history manipulation and behavior exfiltration isn’t just about technical standards; it’s about digital ethics.
We must ask a hard question: if a platform requires trickery to keep your attention, does that content deserve to exist in the first place? As we move toward a more transparent web, we are rediscovering a simple truth: trust is the only metric that can’t be hacked.
In the ongoing battle for your attention, the most dangerous tools are the ones you can’t see—but increasingly, the browser is learning to shine a light into the shadows.
Discover more from TechResider Submit AI Tool
Subscribe to get the latest posts sent to your email.



