1. The Illusion of Digital Safety
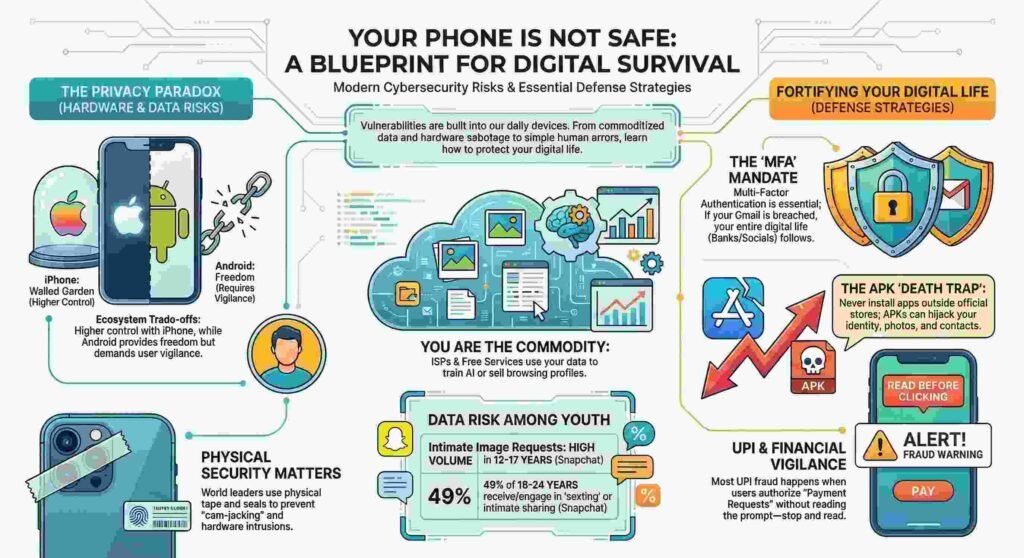
Your smartphone is a voluntary tracking device you pay to carry. We live under the comforting delusion that biometrics and “military-grade” encryption have turned our pockets into private vaults. They haven’t. If you want to see the reality of digital insecurity, look at the devices of those whose lives depend on it. When the Israeli Prime Minister appears in public, his phone isn’t just protected by a passcode—it’s physically modified with tape. This isn’t paranoia; it’s an expert’s acknowledgment that software is a fallible shield. Using the analytical lens of Murali Mastaru, a veteran of digital forensics, we are pulling back the curtain on the hidden vulnerabilities of your digital life.
2. Truth #1: The Six-Year Sabotage (Lessons from the Pager Attack)
High-level state-sponsored warfare doesn’t happen overnight; it is a game of extreme patience and meticulous reconnaissance—or “Rikki.” The recent Israeli operation involving pagers is a chilling example. This wasn’t a remote software hack; it was a supply-chain infiltration six years in the making.
The attackers spent years observing the target’s buying criteria. They established a dummy intermediary company in Europe (Poland or the Czech Republic) to facilitate an order for pagers manufactured in Taiwan. These devices were physically modified during production: tiny explosive charges were placed near the batteries. Forensic analysis shows these pagers were slightly larger than standard models to accommodate the hardware, yet they were sold at a discount to ensure they reached the target units. The operation sat dormant for over half a decade until a specific signal triggered a lateral distribution of destruction.
“Planning means creating a company 6 years in advance… They waited until they needed it, sent a specific signal, and eliminated the target units.”
3. Truth #2: Why the Israeli Prime Minister Tapes His Phone
Physical security provides a “hard stop” that software cannot replicate. When the Israeli PM uses his phone, observers have noted two distinct physical countermeasures:
- Cam-jacking Prevention: A vertical strip of tape covers the “camera island.” In an era of “click-less” exploits, hackers can activate your camera and microphone without a single notification. Tape ensures that even if a state-actor gains total control of the device, they are greeted only by a black image.
- Tamper Indicators: Small marks or tape are placed over screws and seams, acting as a modern-day wax seal.
As Mastaru explains, a world leader can’t perform a forensic sweep every time they pick up their phone. Instead, they look at these physical seals. “If the wax is broken, someone tried to get in last night.” If those marks are disturbed, the device is compromised.
4. Truth #3: The “Walled Garden” is a Golden Cage
The debate between iPhone and Android isn’t about cameras—it’s about autonomy. Apple operates a “Walled Garden,” where they control the hardware, the OS, and the App Store. While this offers superior “out-of-the-box” security for the average user, it comes at the cost of digital freedom.
In India, a staggering 97% of the population uses Android. This makes Android the primary target for hackers—not necessarily because it is weaker, but because that is where the “target population” lives. However, for a security professional, the iPhone’s total control can feel like a restriction.
“I am a person against slavery… I paid for the phone, I should decide how to use it. In a walled garden, you do only what they tell you.”
The danger isn’t the OS itself, but the user’s behavior. An Android user who avoids unauthorized APKs is often more secure than an iPhone user who blindly trusts a closed ecosystem.
5. Truth #4: Your ISP is a Data Broker
Whether your OS is closed or open, the pipeline—your Internet Service Provider (ISP)—remains a massive vulnerability. Every DNS request you make is a breadcrumb. ISPs like Airtel or Tata know exactly who you are, your IP address, and your entire browsing history.
This isn’t just technical logs; it’s a commodity. ISPs package your demographics—where you live, your estimated income, how often you use grocery apps—and sell this behavioral data to third parties. To reclaim your privacy, you must bypass the ISP’s eyes. Use a VPN or switch to secure, third-party DNS services like 8.8.8.8 (Google) or 1.1.1.1 (Cloudflare), which are less likely to sell your identity as a product.
6. Truth #5: You Trained the AI with Your “Private” Life
The reason modern AI can identify a “Nano Banana” or a specific breed of dog in your photos with terrifying accuracy is because you trained it. For over a decade, we accepted “free” cloud storage in exchange for our most personal data.
Google Photos didn’t just store your memories; it used your manual labels and private images as a foundation for their AI algorithms. Every time you searched your gallery for “dog” or “beach,” you were validating their training sets. Today, if you use “AI assistants” in your email or gallery, remember: the system must “look” at your data to help you. The 10 years of free service was never a gift; it was a recruitment.
7. Truth #6: Intelligence is No Shield Against Greed
The most frequent victims of financial fraud aren’t the uneducated; they are Chartered Accountants, IT professionals, and AI specialists. The vulnerability isn’t a lack of technical knowledge—it is “absolute greed.”
Scammers leverage the dream of “fast money,” hijacking the senses until the victim can already see an S-Class Mercedes parked in their driveway. This greed overrides logic, leading smart people to install malicious APKs that “download their entire life.” Once installed, these apps perform a total sweep of contacts, private photos, and relationship data, which are then used for brutal blackmail and extortion.
8. Truth #7: The “View Once” Fallacy and the Government Backdoor
Features like “View Once” on WhatsApp or “Vanish Mode” on Snapchat provide a dangerous sense of security. They are designed to make you feel happy, not to protect your data. Even if the software blocks a screenshot, it cannot close the “Analog Hole.” Any image displayed on a screen can be captured by a second physical camera.
Furthermore, the “end-to-end encryption” shield has cracks. It is an open secret in the industry that the Indian Government has official access to WhatsApp server keys for transcripts used in IT and Tax raids.
“If it is on the internet, it is never safe. ‘View Once’ is just a feeling… it doesn’t actually protect the data.”
9. Conclusion: The Path to Digital Hygiene
True security is not a product you buy, but a habit you maintain. In a world where your digital footprint is more valuable than your currency, you must adopt basic “digital hygiene”:
- Enforce Multi-Factor Authentication (MFA): Passwords are easily stolen. MFA is the only thing that blocks an attacker from hijacking your account once they have your credentials.
- Audit Your Footprint: Every “smart” device—from your fridge to your Alexa—is a potential entry point for reconnaissance.
- Kill the “Free” Mindset: If an app offers “fast money” or “free” premium services via an APK, it is a Trojan horse.
Discover more from TechResider Submit AI Tool
Subscribe to get the latest posts sent to your email.


