Comprehensive Resources for Tech Enthusiasts
About Us
Discover the Story Behind TechResider’s Innovation and Passion
Emoji Mixer Tool
ZeroGPT AI Content Detector
What is an AI Headshot Generator?
Google Search Suggestions Generator
Clickbait Title Generator
AI Ad Generators – Digital Marketing in 2025
AI Text Generator For Content Creation
Image Analyzer – AI Visual Data Analysis
7 Strong Methods to Add Text on Images Online
AI Coder Changing Way Coding
Mind Blowing AI Video Generator 2025
7 Mind-Blowing Ways an Imagination Generator Will Transform Your Brainstorming Forever
Transform Your content Writing with Paraphrasing Tool
Transform Your Content with the Infographic Generator
AI Desk
Power of Image Generators: How They’re Uplifting Creativity in 2025
Why You Should Care About AI Content Rewriters in 2025
AI Article Generator
AI Graph Generator—the future of creating graphs and charts in a completely new way
AI Invoice Text Extractor: Revolutionize Your Invoice Management
Perfect Twitter/X Profile Creator: Tips, Tricks, and Strategies for 2025
Social Media Caption Generator AI
15 Expert Tips on How to be a Great Listicle Writer for Higher Content Engagement
AI paragraph generator 2025
Webpage AI Summarizer
Catchy Slogan Generator
FAQ Generator
Meta Description Generator
Reddit Discussion Generator
Short Story Creator
WooCommerce Product Comparison Generator
Landing Page Creator
SEO content writer
Blog Generator
Viral Post Generator 2025
Twitter Engaging Tweet Generator
The Rise of Micro VCs: Challenging the Status Quo in Venture Capital
LinkedIn Post Generator
Dreamina AI: Unleashing Your Creative Vision with CapCut’s Revolutionary Image Generator
Lifesight Marketing Measurement Tool 2024
InstaDoodle AI Doodle Creator – Video Marketing
Composio – AI Toolset Resource
Trending Web stories
Make Your Infographic Stand Out: Submit Infographics Now
Explore, engage, and elevate your tech knowledge with us.
Tech Insights
Have a Look on Our Free AI Tools Below
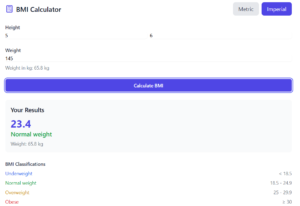
BMI Calculator – BMI: A Simple Guide
So, what’s BMI? It’s a number from your height and weight. It tells you if your weight is okay. It’s like a little check-up. How to Find Your BMI The math is easy: BMI = weight (kg) / height (m) * height (m)…
Gemini AI Content Writer
Google Gemini AI : A Simple Overview Google Gemini AI, a cutting-edge artificial intelligence (AI) platform, has emerged as a transformative force in various industries. This comprehensive overview delves into the capabilities, applications, and implications of this groundbreaking technology. Gemini is a multimodal…
Real Estate Property Description Generator
The particular strength of a meticulously created property description remains fundamental within the real estate industry. During listings of real estate property types ranging from cozy homes to contemporary buildings to prominent estates your written information stands as their initial point of exposure…
Image Resizer: Ultimate tool Effortless Picture Management
Image resizers represent software applications which enable users to modify their image dimensions. Image resizing programs enable you to modify dimensions in digital images. Basically speaking an image resizer functions as software that lets you change image measurements. Through image resizer applications you…
Home Insurance Premium Calculator
How Much will House Insurance Cost? Actually, figuring out house insurance can be hard. But, a Home Insurance Premium Calculator can help! It’s like a magic tool to see how much money you need for insurance. So many things make the price go up or down….
Net Worth calculator : A Guide to Calculating Your Net Worth in 2025
The basic building block of good financial management is knowing your net worth yet it proves hard for professionals to measure correctly. This guide explains how net worth calculators help you gain total control of your finances and make accurate decisions. Understanding Net…
How to Use a Scholarship Eligibility Calculator to Secure Your Academic Future
Finding scholarships that align with your profile requires the same difficulty level as searching for a needle in a haystack. Educational funding possibilities become more essential than ever because college expenses continue their upward climb. This full guide explains how scholarship eligibility calculators…
What Is a GPA Calculator ?
The academic journey depends heavily on essential knowledge about Grade Point Average (GPA) alongside its monitoring systems to both improve present academic outcomes and secure future career options. The guide includes complete information about GPA calculations with expert advice for enhancing your academic…
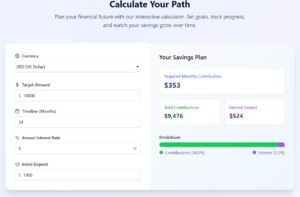
Marketing Budget Planner : Guide to Maximizing ROI [+ Free Tool]
Current business evolution demands marketing budget planning to become sophisticated. As I reflect on the challenges modern marketers face, I’m struck by a compelling statistic: A recent study found that firms which adopt structured budgeting for marketing reach 27% better ROI than organizations…
Profit Margin Calculator Guide: 7 Proven Strategies to Maximize Your Business Profits in 2025
In today’s competitive business arena, you need to know your profit margins. As a matter of fact, in order to survive, such knowledge proves indispensable for any entrepreneur, be it a startup founder or an established one. Mastering the art of profit margin…
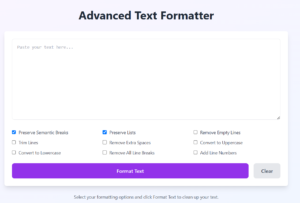
Advanced Text Formatter Features That Will Transform Your Writing Forever
Every writer’s journey begins with raw text, but the magic happens in the formatting. Advanced Text Formatter (ATF) has revolutionized how professionals and casual writers alike transform their plain text into polished, professional content. But what makes this tool truly indispensable in 2025’s…
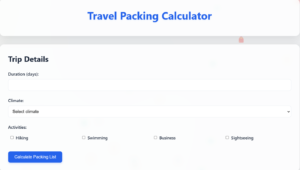
Packing Secrets That Pro Travelers Never Share (+ Free Checklist Generator)
Struggling with overpacked suitcases and forgotten essentials? You’re not alone. According to recent travel industry data, 62% of travelers admit to overpacking, while 45% regularly forget crucial items. But here’s the fascinating reality: master travelers have developed a near-scientific approach to packing that…
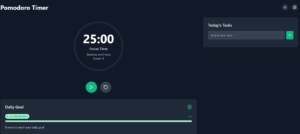
Transform Your Productivity: Pomodoro Timer Technique 25-Minute Secret To Get More Done
In today’s whirlwind world, almost everyone encounters the constant warfare against procrastination and decreasing productivity. What would you say to a scientifically-supported method that guarantees to change all this in less than 25 minutes? All hail the Pomodoro Technique- a time-management technique that…
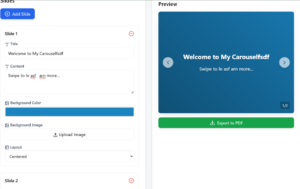
What is a Carousel Generator?
A carousel generator is an online tool designed to help people create multi-slide posts. Generally, the applications of carousel posts are found in social media such as Instagram, LinkedIn, and Facebook . In the carousel posts, the users get the ability to swipe…
Wellness Program Budget Calculator
It will require an understanding of the program’s goals and resources to create a budget for a wellness program. Here’s a guide on how to do it effectively.
Wellness Program Budget Calculator
Program Details
Program Priorities
Budget Allocation Results
Physical Health
$0
$0 per employee
Mental Health
$0
$0 per employee
Preventive Care
$0
$0 per employee
Work-Life Balance
$0
$0 per employee
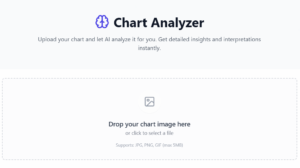
Chart Analyzer: 5 Game-Changing Ways It Can Skyrocket Your Data Insights
Chart Analyzer, it’s a highly effective tool with the power to translate complicated datasets into actionable insights for easy use.A Chart Analyzer is a data visualization tool that enables users to analyze charts, graphs, and other visual representations of data. It allows for…
AI Illusion Creator: Merging Reality and Perception
Imagine a world in which artificial intelligence creates illusions to challenge the reality in our perceptions. The AI Illusion Creator is an innovative tool that is capable of blurring the boundaries between the real and the imaginary to offer unique experiences in visual…
7 Powerful Ways an Image Editor Can Transform Your Content and Boost Engagement
One way to stand out is through the use of high-quality, eye-catching visuals—and that’s where an image editor comes into play. Whether you’re a social media manager, blogger, or small business owner, an image editor can be your secret weapon for creating stunning graphics, enhancing…
UTM Builder: Complete Guide to Monitoring Your Marketing Campaigns
The digital marketing world has started becoming more and more data-driven; businesses and marketers want to see effective ways to track their campaigns. Enter the UTM builder, a simple but powerful tool for generating UTM codes on the tracking of marketing efforts. The…
Free Mind Map Visualization Tool
A mind map is a powerful visual tool used for organizing thoughts, brainstorming ideas, and solving problems. But what makes mind maps even more effective is the tool you use to create them—a mind map creator. Whether you’re a student trying to structure…
What is a Schema Markup Generator?
In the world of SEO, a schema markup generator is a pretty powerful tool for your website. So, what is it, anyway? Schema markup generator refers to a tool that enables the creation and application of structured data on your website. Using particular…
SIP Calculator: A Complete Guide to Understanding and Using It
Introduction to SIP Calculator When it comes to investing, everyone is looking for a simple, effective way to plan and track their investments. This is where an SIP Calculator (Systematic Investment Plan) comes in handy. Whether you’re a beginner or a seasoned investor,…
Best Profile Picture Maker in 2025
Whether you are building your personal brand, business, or just keeping up with your professional online presence, your profile picture says a lot even before you’ve typed a single word. Let us dive into the world of profile picture makers to see how…
Free Resume Builders: Create a Professional Resume Without Breaking the Bank
What Are Free Resume Builders? In today’s competitive job market, having a well-crafted resume is essential for standing out among other candidates. While professional resume writing services can be expensive, free resume builders offer an accessible alternative for job seekers. This comprehensive guide…
Enhanced Featured Image Maker
A Featured Image Maker is a tool or service that allows you to generate images that will work as featured images for your blog posts, articles, or social media content. Turn Words into Eye-Catching Images – Enhanced Featured Image Maker These are the…
Markdown to HTML converter Online
Markdown to HTML Converter A markdown to HTML converter is a converter that changes the text written in Markdown syntax to HTML code. Markdown is a lightweight markup language that uses simple formatting such as an asterisk for bold or italics and hashes…
SEO ROI Calculator
SEO ROI Calculator
Results
Monthly Revenue:
Monthly Profit:
ROI:
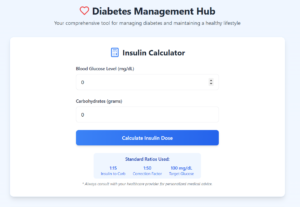
Insulin Calculator
Managing diabetes is a task that requires great accuracy and care. One such innovation in the world of diabetes management is the insulin calculator. This guide will delve into how this new technology makes diabetes management more accurate, convenient, and less stressful for…
Life Coaching Cost Calculator
Credit Card Interest Calculator
Credit card debt is one of the most pressing financial issues for many. Ever wondered how much interest you are paying on your credit card balance? Well, you are not alone. The good news is that there is a Credit Card Interest Calculator…
Business Insurance Cost Calculator
Running a business is not without its responsibilities. One of the most important, however, is securing the right business insurance. While it is an essential step in safeguarding your company from unforeseen risks, the cost of insurance can vary quite widely depending on…
best aI social media post generator
[wpaicg_prompt id=14930 custom=yes] AI Social Media Post Generators use artificial intelligence to help create posts. These tools can save you lots of time and effort while making cool posts people want to read. What do these AI social media post generator tools do?…
AI Instagram Caption Generator
An AI Instagram caption generator is a tool that uses artificial intelligence (AI) to generate captions for your Instagram posts. These captions are designed to be engaging, creative, and effective in boosting your content’s visibility and interaction. [wpaicg_form id=14433 settings=no custom=yes] Provide Context:…
Career Development Advice Tool: A Simple Guide to Growth & Success
Career development is a journey of learning & growing in your job life. It’s not just for newbies; even if you’ve been around a while, figuring out your career path is super important for staying successful. So, what’s career development all about? Why…
Loan Repayment Calculator
Loan Repayment Calculator
Results
Monthly Payment: $
Total Interest: $
Repayment Schedule
| Month | Payment | Principal | Interest | Balance |
|---|
Mortgage Calculators: Your Essential Home Buying Tool
Of all the methods that put at your disposal when you are searching for a house to buy, the most effective one is definitely the mortgage calculator. Here is a web-based assistant that is created with the purpose of explaining all those details…
OCR Tools Unleashed: Maximizing Text Recognition Potential
How Optical Character Recognition (OCR) Can Transform Your Business Operations In today’s digital age, businesses deal with massive amounts of data daily. Manually processing this data can be time-consuming and prone to errors. This is where Optical Character Recognition (OCR) tools come in…
Adobe Premiere-Video Editing Amongst After Effects, Final Cut Pro, and DaVinci Resolve
Unveiling the World of Adobe Premiere In the realm of professional video editing, the selection of a tool holds paramount importance for translating creative visions into reality. Amidst the diverse array of video editing options, Adobe Premiere emerges as a standout choice, embraced…
Top Voice to Text Generators 2024: Transforming Speech into Text
The Voice to Text Generator, a tool that has revolutionized the way we convert spoken language into written text. In this comprehensive guide, we will delve deep into the world of Voice to Text Generators, exploring their functionality, applications, benefits, and the various…
Best Age Calculator Online 2025
Age calculator
Calculate Age from Date of Birth
How Old Am I? How many minutes old am I? Calculate Your Age1. Calculator:
2. Calculator:
"); true_bodyobject.cakewnd.document.write(""); true_bodyobject.cakewnd.document.close(); } } What is an Age Calculator Online? An age calculator online is a digital tool designed to determine your age based on your birth date and the current date. With just a few clicks, you can obtain accurate information regarding your years,…
Why Choose Us
Unique Value Proposition
The Future of AI Market: Analysis of the $990 Billion Industry
The Growing Demand for AI Factors driving the growth of AI market Statistics on the growth rate…
The Evolution of AI Influencers: A Look at Miss AI Pageant
Introduction to AI Influencers In the rapidly evolving virtual panorama, synthetic intelligence (AI) has permeated…
Experience the magic of Artificial Intelligence in shaping User Experience
Artificial Intelligence (AI) plays a crucial role in enhancing user experience across various digital platforms….
Elevating Apple’s Artificial Intelligence Game: Exploring Potential Partnerships and Innovations
In the dynamic realm of technological innovation, staying beforehand of the curve is paramount. Apple,…
Lepro’s LightGPM™ Technology is Revolutionizing Smart Lighting
Get prepared to revel in lighting fixtures like in no way before! Lepro, a frontrunner…
AI Revolutionizing Smartphone (AI Phones) Technology
AI Phones: The Next Generation of Smartphones Powered by Artificial Intelligence From the halls of…
How do I submit an AI tool?

To submit an AI tool, typically you would:
Find a reputable AI tool directory or marketplace
Create an account on the platform
Fill out a submission form with details about your tool
Provide any required documentation or demos
Submit for review and approval
How many AI tools are there?

The number of AI tools is constantly growing. As of 2024, there are thousands of AI tools available across various categories such as:
Natural Language Processing
Computer Vision
Data Analysis
Generative AI
Robotics
and many more
The exact number is difficult to pinpoint due to rapid development in the field.
Can AI replace web developers?

AI can assist web developers but is unlikely to fully replace them in the near future. AI tools can:
Generate basic code and layouts
Assist with design elements
Automate repetitive tasks
However, web developers are still needed for:
Complex problem-solving
Understanding client needs
Ensuring accessibility and user experience
Integrating various systems and technologies
Maintaining and updating websites
Can AI create websites?

Yes, AI can create basic websites. There are AI-powered website builders that can:
Generate simple layouts and designs
Create content based on user input
Suggest color schemes and typography
However, for more complex or custom websites, human developers are still necessary to:
Implement specific functionality
Ensure brand consistency
Optimize for performance and SEO
Create unique, engaging user experiences
AI is a tool that enhances web development rather than completely replacing human expertise.
Why can’t AI replace humans?
AI cannot fully replace humans due to several limitations:
Lack of true understanding and contextual awareness
Inability to experience emotions or empathize
Limited creativity and original thinking
Absence of moral reasoning and ethical judgment
Dependence on human-generated data and programming
Will AI replace technical writers?

While AI can assist with certain aspects of technical writing, it’s unlikely to completely replace human technical writers because:
Technical writers often need domain expertise and ability to interview subject matter experts
They require understanding of audience needs and ability to tailor content accordingly
Complex documentation often needs a human touch for clarity and coherence
AI may struggle with creating truly original technical content or handling unique scenarios
What is AI Tool Submit?
AI Tool Submit is a platform designed to help individuals and businesses showcase their artificial intelligence (AI) tools to a wider audience. It acts as a directory where users can discover and explore a variety of AI-powered applications.
Can AI replace software developers?

AI is unlikely to fully replace software developers in the near future:
Software development often involves collaboration and communication skills that AI currently lacks
Complex problem-solving and system design still require human creativity and insight
AI tools can assist in coding but lack the ability to understand broader business context and requirements
How is AI taking over the world?

AI isn’t literally “taking over the world,” but it is becoming increasingly prevalent:
Impact on privacy, security, and ethical considerations in society
Integration into various industries (healthcare, finance, manufacturing, etc.)
Automation of routine tasks and decision-making processes
Advancements in natural language processing, computer vision, and robotics
Influence on job markets and skill requirements
How many AI websites are there?

It’s impossible to give an exact number as it’s constantly changing. There are thousands of websites related to AI, including:
AI educational resources The number continues to grow rapidly as AI technology advances and becomes more mainstream.
AI research institutions
AI companies and startups
AI news and information sites
AI tool and service providers
What They Say